Phishing is the attempt to get a persons information like Username, password, bank account details or more through fraudulent meant by disguising one as whom they are not.
While scam email or fraud email is trying to get money or other valuable items by promising to offer a value which does not exist.
These emails are the most prevalent cyber crimes that are perpetrated through emails. With Phishing emails you would get an email that appears to have come from you bank, Paypal, Apple, Amazon, Ebay or from other companies that you might be using and they usually claim that your account has been compromised and that you are required to click a link in the email to rectify your account and resolve the issue.
The only problem there is that if you click on the link it would take you to a website that they have created to look like the company that they claim you use and require you to input personal details of the account that you hold which as you are entering the details they are all being collected in their database for use to compromise your account and security.
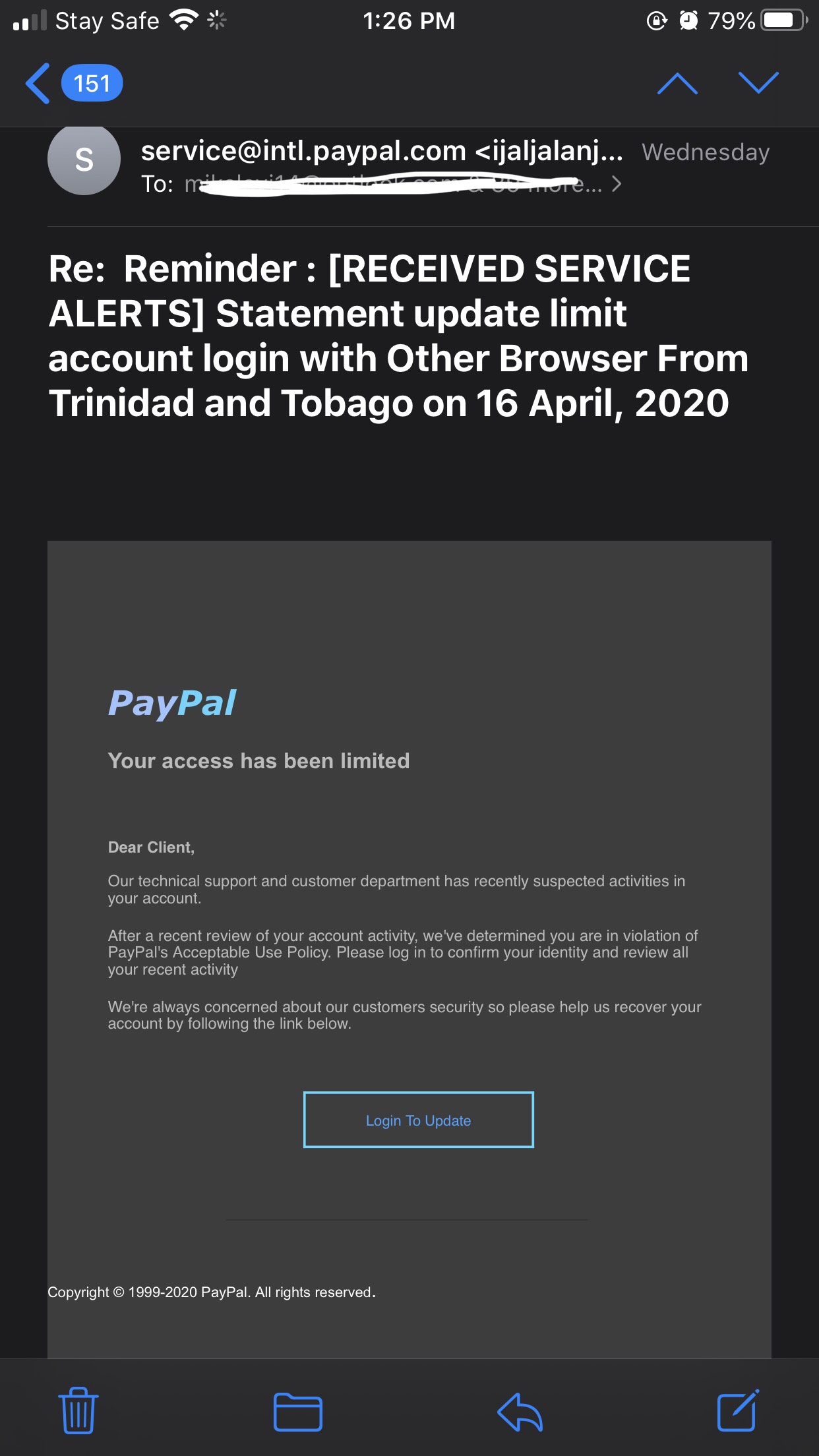
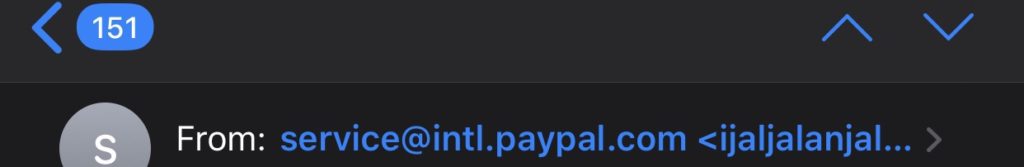
Phishing emails are usually easy to detect but most people out of haste tend to over look the from address and go straight to the content of the mail. The people that send out phishing emails in an effort to reach a lot of people use mass mailer apps and systems. Email clients like outlook, apple mail, thunderbird in an effort to make new emails easy to identify reads the email header which they can spoof the name to appear as Amazon, Ebay or Paypal so in the email client the header can give the spoofed details.
Scam emails are very easy to catch and most time they gain by exploiting well meaning individuals. The emails can appear to come from someone in need of assistance claiming that they need support, or a lonely beautiful girl that wants a handsome man to marry or even the most common “The Nigerian Prince”. These mails are less common now but usually make it to the inbox as the person sends it from a valid email address. Best practice is to make sure that if you want to donate, always go through an NGO, if you get the email, advice the person to seek help from the proper authorities. In the case of marriage, DO NOT GIVE MONEY TO SOMEONE YOU HAVE NOT SEEN OR MET FACE-TO-FACE. Lastly, if you get an email from a “Nigerian Prince” just delete it.
Example email from header
From: Paypal <[email protected]>
The email client reads the name identifier and resolves it to show as coming from Paypal and if the user doesn’t investigate further might act on the email and fall victim of the phishing hack.
Best Practices to Avoid Email Attacks
- Always use a trusted email provider. Providers like Google (Gmail), Microsoft (Outlook), Yahoo offer very good phishing detections systems. they analyze the header (Source IP Address, Source Domain, mail encryption, etc), they analyze the source domain for DKIM, SPF records to know if the source is trusted. If they lack any of these parameters, the mail is sent to the spam or junk folder. Sometimes legit emails are sent to junk folders due to misconfigured records. So, try to check your junk and spam sometimes.
- The provider does not always catch all scam of phishing emails as they use a “Known Threat” record to analyze and filter. Also, the use might still fall prey when they look in the Spam or Junk folder. In that case, make sure to look at the email address. Click on the “From” name to see the actual name of the sender. The domain must be that of the sending company, if in doubt go to google and find out the website. eg. Amazon website is https://www.amazon.com/ the domain is amazon.com and any email from them must end with @amazon.com or @xyz.amazon.com (the XYZ means a sub domain, the most important is the primary domain name).
- When still in doubt, review your past activities. Try to remember the last activities you performed on the sites to know if it matches with the claims in the email.
- If you still have any lingering doubts, ALWAYS CONTACT THE SUPPORT OF THE COMPANY. Every business has a customer support, reach out to them and send them a copy of the email you received to verify f it came from them or call their customer care number on their website or reach them on their social media handle. Do not be in a hurry and wait for a response. Most companies reply to emails in 24hours.
- Use a strong password, if you are not sure, use a password generator. Don’t worry about forgetting your long passwords, all major browsers offer to remember login credentials (Best practice: if you are using chrome, make sure you sign-in with your gmail address and enable sync. for mozilla and opera, create an account with them and make sure that it syncs to the cloud. this is to make sure that even when you reformat the system or loose it, you can always retrieve your passwords).
- ALWAYS USE 2FA (2 Factor Authentication). this is the most important thing anyone can use to secure any account because even if your username and password are compromised, the hacker would still need the 2nd factor of authentication which i always use Google authenticator and microsoft authenticator.
Major companies offer websites or email addresses where we can all report phishing or scam mails. This is very useful as it is used to analyze and update the “Known Threat Index”. These emails are available below. You can contact us if there is any company you would like to get their reporting email. or website
- Google: https://support.google.com/mail/contact/abuse
- Microsoft: [email protected]
- Amazon: [email protected]
- Paypal: [email protected]
- ebay: [email protected]
- Anti-Phising Working Group: [email protected]